Draytek 2860 and Unifi USG
I normally don’t do networking posts but in this case I think there may be a need as I could not find any solutions for this anywhere else.
This solution uses a Draytek 2860 as a VDSL modem, VPN and LAN-LAN device.
Using a Draytek 2860 as modem and Unifi USG as gateway is not without it’s problems.
Why using Draytek as modem:
- Draytek is a modem working well with a BT FTTC VDSL connection
- Draytek is great for client VPN and LAN-LAN connections both using IPsec
- Draytek and USG can always be reached via the client VPN access – so accidental lock-out is (almost) impossible
Why using Unifi USG as gateway:
- Unifi USG provides great network management via the Unifi controller
Problems to be solved with the solution below:
- USG is in a double-NAT situation
- Solved with DMZ on Draytek
- Draytek incoming VPN wants to route through itself bypassing the USG
- Solved with policy route on Draytek forcing USG gateway
- Draytek has two DMZ modes and only one works:
- Solved by using “Private IP” DMZ
- Private IP: semi-NAT mode where some functionality works
- Works: modem, VPN, LAN-LAN and remote router management
- Does not work: Port forwarding (makes sense)
- True IP: bridge mode where Draytek only works as modem
- Works: modem
- Does not work: everything else
- Port forwarding to WordPress Server
- Solved by using port forward on Unifi USG
- Route VPN and LAN-LAN around the DMZ
- Draytek LAN1 to USG LAN direct connection via switch
- USG WAN2 could have been used but this is better to use for WAN failover
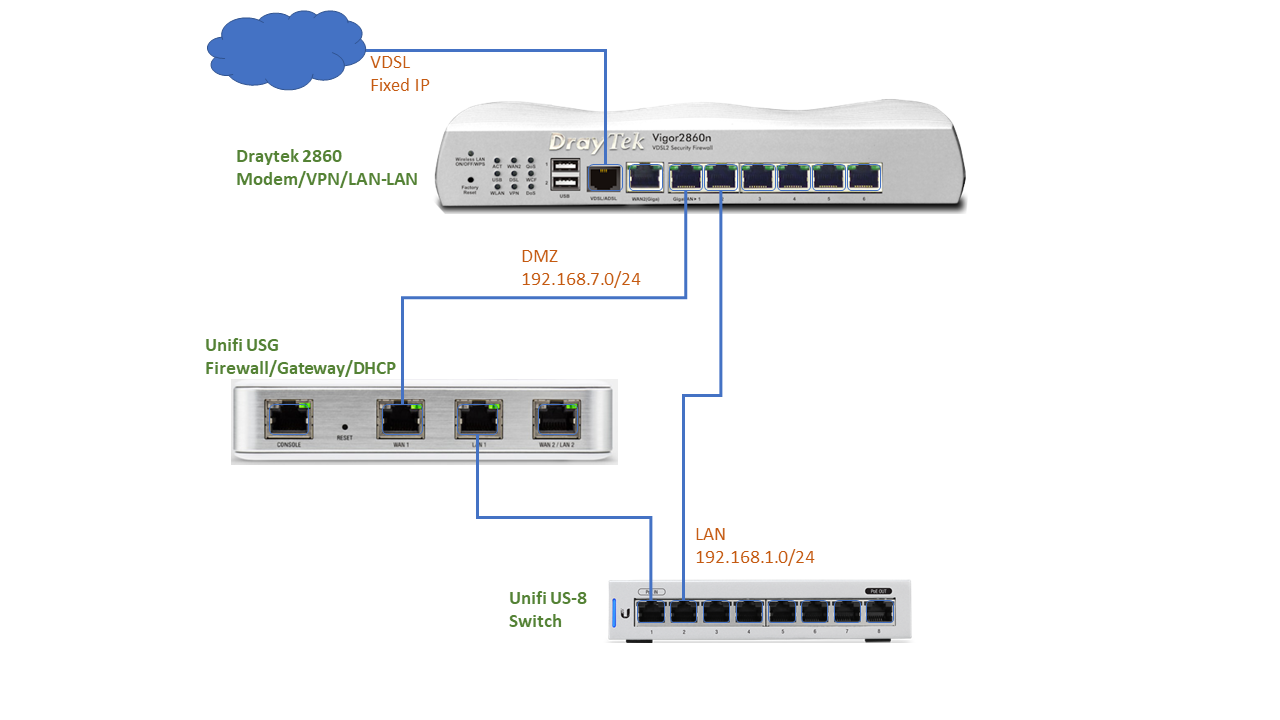
Connection diagram:
Draytek Setup (relevant to this scenario):
- WAN: nothing special to do
- LAN: create two networks: DMZ and LAN1:
- DMZ network: semi-NAT network to Unifi USG
- For NAT Usage
- IP Address: 192.168.7.3
- DHCP Enable Server
- Start IP address: 192.168.7.100 (USG WAN)
- Gateway IP: 192.168.7.3
- LAN1 network: This is used to route around the DMZ
- For NAT Usage
- IP Address: 192.168.1.3 (as the USG is 192.168.1.1)
- DHCP Enable Relay
- DHCP Server IP: 192.168.1.1 (USG LAN)
- VLAN: map your LAN1 to port 2 (port 1 is reserved for DMZ)
- DMZ network: semi-NAT network to Unifi USG
- Routing: create a route policy for LAN1
- Load-Balance/Route Policy:
- Protocol: Any
- Source: IP Subnet: 192.168.1.0/24
- Destination: Any
- Destination Port: Any
- Interface: LAN1
- Specific Gateway: 192.168.1.1 (USG LAN)
- Priority: 100
- Load-Balance/Route Policy:
- NAT:
- DMZ Host: Private IP
- Private IP: 192.168.7.100 (USG WAN)
- Firewall: Disable all (USG is the firewall)
- VPN and Remote Access:
- Remote Dial-in User:
- Allowed Dial-in type: L2TP/IPsec with pre-shared key
- Subnet: LAN1
- LAN to LAN:
- Allowed Dial-in type: IPsec Tunnel
- Local Network IP: 192.168.1.0/24
- …and much more
- Remote Dial-in User:
Unifi USG Setup (relevant to this scenario):
- WAN Networks:
-
WAN:
- IPV4 Connection Type: Using DHCP
-
- LAN Networks:
- LAN:
- Gateway IP / Subnet: 192.168.1.1/24
- DHCP server enabled
- LAN:
- Gateway:
- Port Forwarding:
- Name: http
- From: Anywhere
- Port: 80
- Forward IP: WordPress server IP
- Forward Port: 80
- Protocol: Both
- Port Forwarding:
